
In a report released on August 4, 2022, the Health Sector Cybersecurity Coordination Center (HC3) highlighted the many security risks faced by the IoT market today and provided a list of best practices to secure against them.
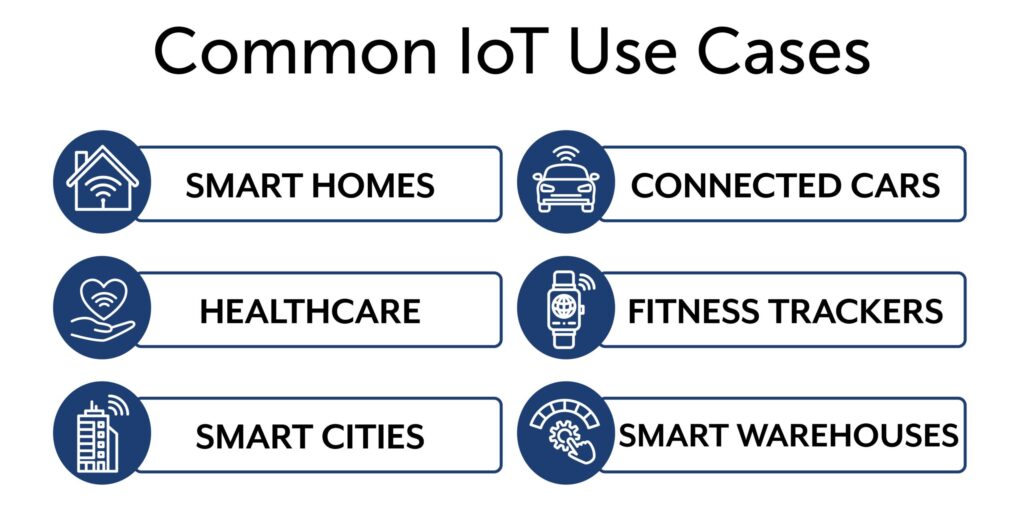
The IoT market is massively expanding with “7 billion devices [already] connected through IoT” with an estimated “20 billion more to come by 2025,” mentioned in the report. With some common uses including smart homes, fitness trackers, and cars, the IoT market is becoming even more accessible and common in people’s daily lives. However, as the IoT network expands, the number of security threats does as well. With large industries such as finance and healthcare implementing this technology, it is imperative that the proper security measures are taken to protect these systems.
David Gomes, Chief Operating Officer at Eclypses says, “With the ever-expanding landscape of IoT demonstrating incredible benefits to daily life, it is imperative to create consistent security across a network to defend against bad actors. Resource–constrained IoT devices are oftentimes less secure making them a prime target for network entry. MTE offers a consistent, compact, and efficient cyber security solution for all devices and IoT networks, all the way down to an 8-bit microcontroller.”
The HC3 report states, “with the implementation of IoT technology in an organization, users are also widening the attack surface on which they can become a target from threat actors.” It may seem like enough to place all devices on a “flat network” where all accounts are connected on the same network, but if even one device has a vulnerability that is exploited, it opens the ability for hackers to gain access and move through the entire network. Utilizing network segmentation and keeping devices up to date on the latest security are good first steps to minimizing risk to an IoT network, according to the report.
Even after implementing network segmentation, there are still common IoT attacks that hackers utilize to gain access to the networks and steal valuable data. The HC3 report notes common IoT attacks including privilege escalation, man-in-the-middle attacks, brute-force attacks, and distributed denial of services (DDoS) as threats to an IoT network. By taking advantage of unsecured network communications and network vulnerabilities, hackers can utilize these attacks to gain access to a network and take over. Understanding and implementing best practices, including changing default router settings, choosing a strong password, and utilizing a zero-trust model, are just a few of the recommendations this report provides as to how to secure against these threats.
To learn more about how to secure an IoT network and the existing threats, read the report here: https://www.hhs.gov/sites/default/files/internet-of-things-security-analyst-note.pdf
If you have any questions for the Eclypses team, please let us know.


