As multi-factor authentication (MFA) becomes a mandatory security practice, especially for almost all cyber insurance policies, cyber criminals are seeking new ways to break through these walls to steal your data.
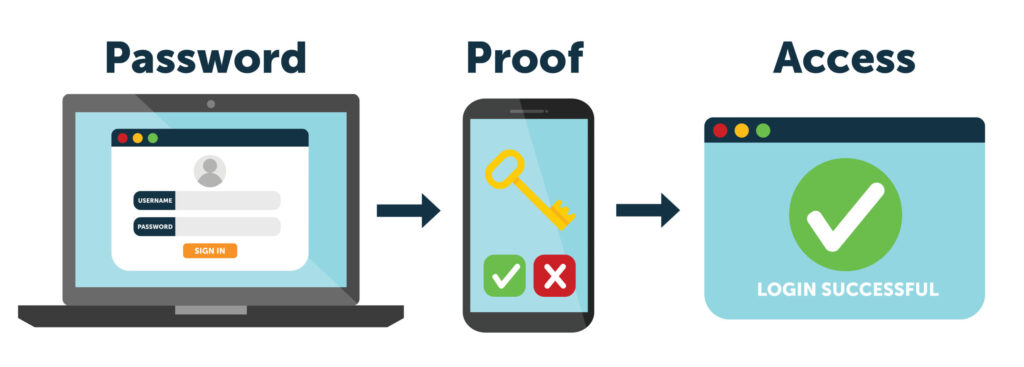
Multi-factor authentication (MFA) is the authentication method that requires the user to provide two or more verification components to gain entry to an asset, such as an application, online account, or a VPN. Two-factor authentication (2FA) is a type of authentication that requires two factors to verify the user’s identity. According to CSO Online, cyber criminals are finding new ways to exploit multi-factor authentication, such as SMS-based man-in-the-middle attacks, supply chain attacks, compromised MFA authentication workflow bypass, pass-the-cookie attacks, and server-side forgeries.
Recent MFA Attacks
In recent news, cyber criminals stole $34M in funds from 483 Crypto.com users. It appears they don’t know exactly how these criminals got by their two-factor authentication. According to American Banker, it seems that Crypto.com, a cryptocurrency exchange company, provided one-time passwords — these are usually six-digit codes provided via text message or in a multi-factor authentication app — to affected users after hackers initiated a transaction from their compromised account. With little information released, it appears to have been an MFA attack. However, it very easily could have been a different vulnerability including a zero-day attack. Luckily for Crypto.com users, Crypto.com said they will be reimbursing customers who were affected by this attack.
Another recent 2FA attack included the company Coinbase, another cryptocurrency exchange company, where more than 6,000 Coinbase users had funds stolen from their accounts after hackers used a vulnerability in Coinbase’s SMS-based two-factor authentication system to breach accounts, according to The Record. Coinbase said that a third party took advantage of a flaw in Coinbase’s SMS Account Recovery process in order to receive an SMS two-factor authentication token and gain access to these accounts.
Cyber Insurance Requirements
Every cyber insurance policy is different, but a majority often address costs associated with operational disruption, data loss, incident response and investigation, crisis management, ransomware payment, and legal expenses.
In recent years, organizations must implement multi-factor authentication as a requirement of their cyber insurance coverage. Without MFA, clients risk non-renewal or a retention hike of 100% or more. In the past, insurers have identified MFA as being among the most effective risk management tools for preventing ransomware attacks, but with cyber criminals producing new ways to bypass MFA, there need to be additional preventions in place.
“Multi-factor authentication is good – but it’s only as good as the way it is implemented or the quality of the third-party provider. I believe we can expect cyber insurance requirements to become stricter in the future, as we continue to see these attacks in the news,” said Joe Jeanjaquet, Eclypses Senior Director of Applied Technologies.
Looking Towards the Future
From these recent attacks, it shows how difficult it is to set up all the pieces of security and have these systems work together correctly. Whether it’s an MFA attack, zero-day attack, or any other common cyber threats out there, it is important to focus on securing the data at the application level. Eclypses MTE technology allows you to control your customer data and stop trusting things you do not control, like third-party providers.
Eclypses MTE technology is an easy-to-use data security module that enables consistent security to be easily orchestrated across the entirety of an environment. MTE protects the data as soon as it is generated to remove the data exposure risk that is associated with setting securities up incorrectly or zero-day vulnerabilities in the operating system or communication protocol.
“MFA and 2FA are not enough, it needs to be used in a more sophisticated way than it is currently. The current method of just echoing data back to the server over the communication protocol leaves it very vulnerable. By incorporating MFA into the initialization of a security protocol like MTE it serves a more significant role that enhances the synchronization between endpoints,” comments Aron Seader, Eclypses Senior Director of Core Engineering.



